This semester I’ve been teaching a module that covers a couple of different maths topics, and have been setting little puzzles for my students to complement what they’re learning – and some of them have been quite fun to write and play with. I thought I’d share some of them here, so you can enjoy them too.
You're reading: Posts Tagged: cryptography
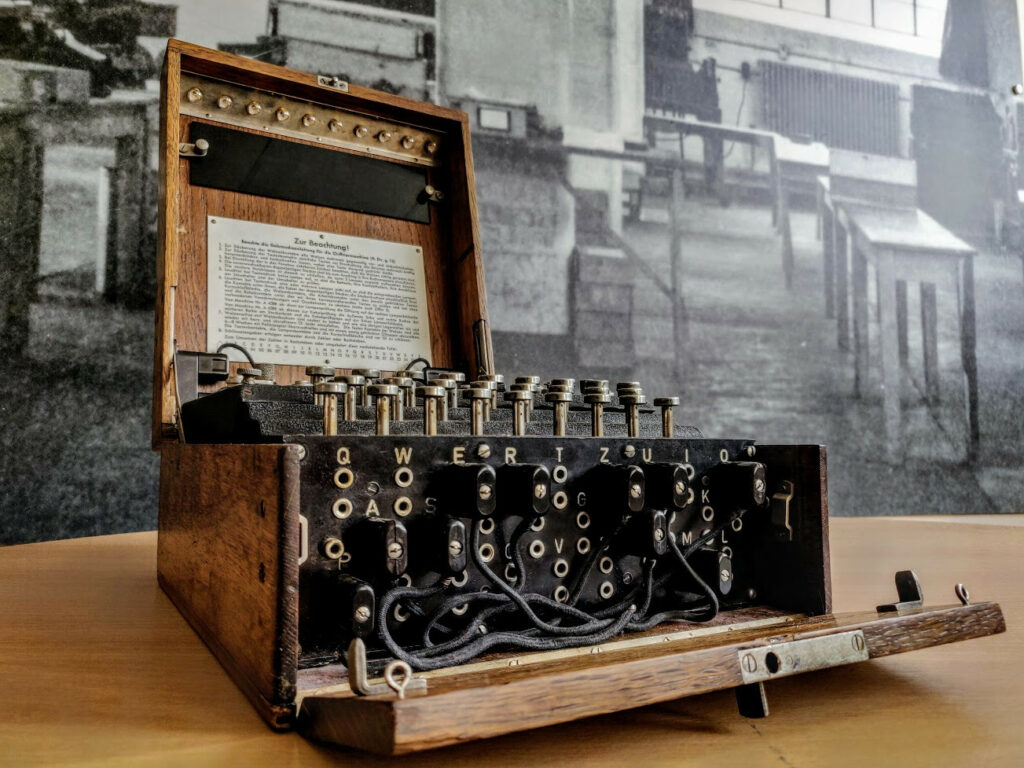
Mathematical Objects: Enigma machine with Tom Briggs

A conversation about mathematics inspired by an Enigma machine. Presented by Katie Steckles and Peter Rowlett, with special guest Tom Briggs.
Podcast: Play in new window | Download
Subscribe: RSS | List of episodes
View D-Day via real-time tweets of Enigma intercepts from Bletchley Park
Bletchley Park are planning to real-time tweet the D-Day landings on their 75th anniversary, via decrypted German Naval Enigma messages intercepted on site.
The Bletchley Park website explains:
To coincide with the 75th anniversary of D-Day, this Thursday 6 June 2019, Bletchley Park will be live tweeting minute by minute, in real time 75 years to the day, decrypted German Naval Enigma messages intercepted on site during the 6 June 1944 operation.
Starting from 23.58 GMT on 5 June, when German naval units were put on alert, to the following night by which time 156,000 Allied troops had landed by sea and air, the messages reveal how the Germans slowly realised that the Allied invasion in the West had begun. The Western Allies had landed in Normandy and not Calais as the Germans had been led to believe.
The 182 messages will be posted on the Bletchley Park twitter account @bletchleypark starting at 00.58 (GMT+1) and ending at 23.38 (GMT+1) – the times they would have originally been intercepted on 6 June 1944.
Update: If you are following the messages, it may be useful to know that Bletchley has produced a glossary of terms used.
Registration for 2019 Alan Turing Cryptography Competition and MathsBombe is open
The Alan Turing Cryptography Competition, now in its 7th year, is an online competition run by the University of Manchester School of Mathematics, for school students up to year 11 or equivalent. Cryptographic puzzles are released every couple of weeks and teams of up to four compete to solve the puzzles, with prizes for the fastest and other randomly selected correct entries. Registrations are open now, and the competition starts on 28th January 2019.
For sixth form pupils, there is also MathsBombe – an online competition, with two mathematical puzzles released every fortnight. The puzzles are not directly related to the A-Level syllabus but will require students to use their problem-solving skills.
Further information
Review: The Mathematics of Secrets by Joshua Holden
 Any book on cryptography written for a more-or-less lay audience must inevitably face comparisons to The Code Book, written in 1999 by Simon Singh, the king of distilling complex subjects to a few hundred pages of understandable writing. While Singh’s book is a pretty thorough history of codes and codebreaking ((I will in this review unapologetically make no attempt to maintain any distinction between the terms code and cipher; cryptography, cryptanalysis and codebreaking, etc.)) through the centuries with plenty of the maths thrown in, The Mathematics of Secrets is tilted (and indeed titled) more towards a fuller explanation of the mathematical techniques underlying the various ciphers. Although Holden’s book follows a basically chronological path, you won’t find too much interest in pre-computer ciphers here: Enigma is cracked on page seventy, and the name Alan Turing does not appear in the book.
Any book on cryptography written for a more-or-less lay audience must inevitably face comparisons to The Code Book, written in 1999 by Simon Singh, the king of distilling complex subjects to a few hundred pages of understandable writing. While Singh’s book is a pretty thorough history of codes and codebreaking ((I will in this review unapologetically make no attempt to maintain any distinction between the terms code and cipher; cryptography, cryptanalysis and codebreaking, etc.)) through the centuries with plenty of the maths thrown in, The Mathematics of Secrets is tilted (and indeed titled) more towards a fuller explanation of the mathematical techniques underlying the various ciphers. Although Holden’s book follows a basically chronological path, you won’t find too much interest in pre-computer ciphers here: Enigma is cracked on page seventy, and the name Alan Turing does not appear in the book.
Maths at the British Science Festival 2016
Next week, the British Science Festival will take place in Swansea, in and around the University. Here’s our round-up of all the mathsiest of the maths events taking place during the week. Our own Katie Steckles will be there introducing most of these events, so you might spot her at the front telling you what to do if there’s a fire. You’ll need to register to book tickets, but all the events are free.
GCHQ has declassified James Ellis’s papers on public key cryptography
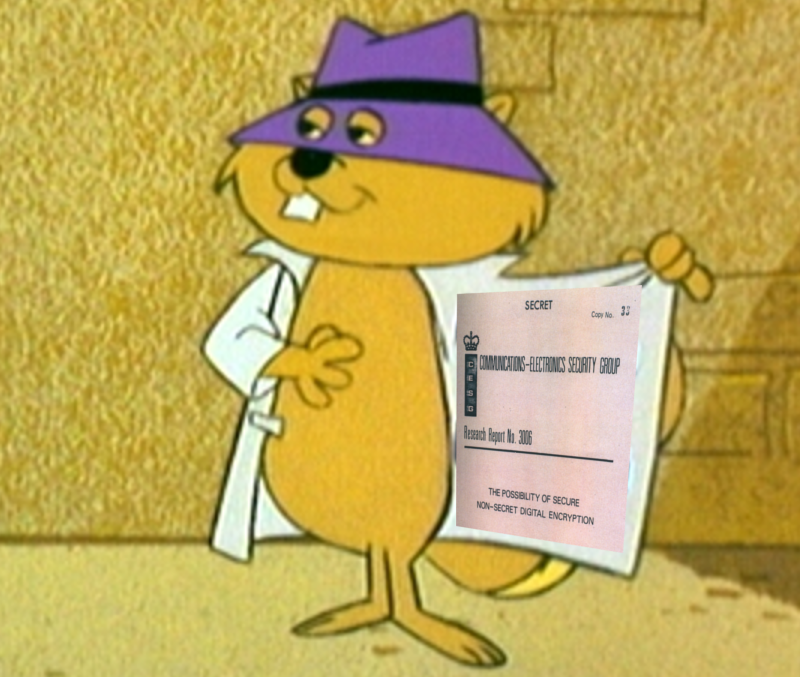
Robert Hannigan, the Director of British intelligence agency GCHQ, gave a speech at MIT recently on the currently contentious issue of backdoors into encryption.
To accompany his speech, and maybe to reaffirm GCHQ’s credentials on the subject, he published two papers written by James Ellis in 1970 about what would become public key encryption: “The Possibility of Secure Non-Secret Digital Encryption” and “The Possibility of Secure Non-Secret Analogue Encryption”.
The story famously goes that two decades after Rivest, Shamir and Adleman announced the RSA algorithm for public key cryptography, GCHQ admitted that their employee Clifford Cocks had come up with essentially the same thing four years before, inspired by James Ellis’s papers on the possibility of cryptography without a secret key.
More information
Rober Hannigan’s speech, Front doors and strong locks: encryption, privacy and intelligence gathering in the digital era.
Read the papers: “The Possibility of Secure Non-Secret Digital Encryption” and “The Possibility of Secure Non-Secret Analogue Encryption” by James Ellis.

